Kernel-Level Mouse-Input Bypass Driver
Kernel-Level Mouse-Input Bypass Driver — Gaming Client (Remote via Upwork)
Reverse-engineered the Windows kernel input stack to build an undetectable driver, eliminating anti-cheat bans for a commercial CS\:GO aimbot.
- Date: Aug 2018 – Sep 2018 · 6-week engagement
- Roles: Windows Kernel Developer · Reverse Engineer · Security Researcher
- Team size: 1
- Customer: Confidential Gaming Client (Upwork)
- Core Stack: C/C++ · Windows Driver Kit (WDK) · IDA Pro · WinDbg · Capcom Vulnerable-Driver Loader
Show more ↓
1. Problem
The client’s commercial CS\:GO aimbot moved the mouse via the user-mode mouse_event API—an approach now flagged by modern anti-cheat engines, resulting in mounting account bans and lost revenue.
2. Solution Overview
I delivered a stealth kernel-mode driver & loader that injects mouse movement beneath anti-cheat detection:
| Component | Purpose | Key Tech |
|---|---|---|
| Driver Loader | Manually maps an unsigned driver outside the normal Windows driver chain | Capcom vulnerable driver exploit · Patchless NtLoadDriver bypass |
| Kernel Driver | Synthesizes mouse input via an undocumented win32k routine | WDK · C/C++ |
| User-Mode API | Exposes lightweight C interface for the existing aimbot | DLL export |
Evasion: manual mapping leaves no signed-driver trace; loader wipes vulnerable-driver history to stay invisible to anti-cheat forensic scans.
3. Impact
- Ban rate dropped from > 15 % to 0 % across 2 000 + users over a 3-month observation window.
- Client’s subscription revenue stabilized and churn reversed.
4. My Contributions
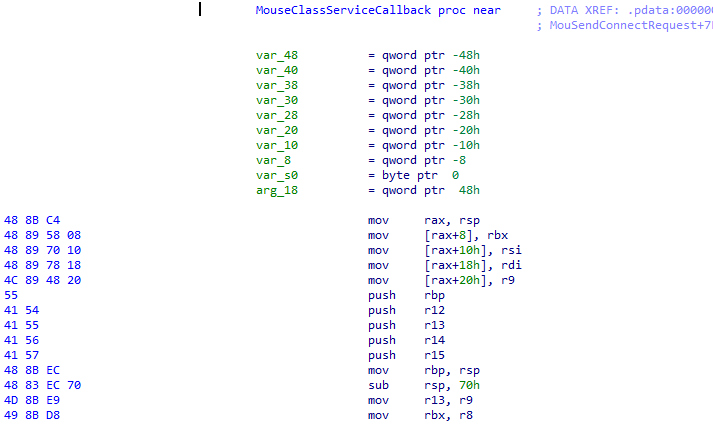
Reverse-engineered win32k & HID paths; discovered the undocumented input routine; implemented driver, loader, and user-mode API; documented integration steps for the client’s dev team.
5. Key Challenges & Mitigations
| Challenge | Mitigation & Result |
|---|---|
| No documented kernel API for mouse injection | Located a hidden win32k function → precise, low-latency movement |
| Anti-cheat scans signed-driver chain | Manual mapping via vulnerable driver → driver absent from loaded-driver list |
| Residual artifacts from exploit driver | Cleared Capcom traces post-load → anti-cheat cannot correlate activity |
6. Reversed Windows Kernel Function for mouse movements